Windows 2000 introduced a new security feature called ‘account lockout’ that disables a user account when a certain number of failed logons occur due to wrong passwords within a certain interval of time. The purpose behind it is to foil any attempt by attackers to brute-force into a user account by guessing the password. If the attacker enters too many bad guesses the account gets locked.
Account lockouts are now a standard feature of many modern operating system as well as web applications such as email and bank logins.
Occasionally, however, Windows can lock out legitimate users from their accounts. Whenever that happens the administrator has to sift through log files, determine the cause and bring everything into order.
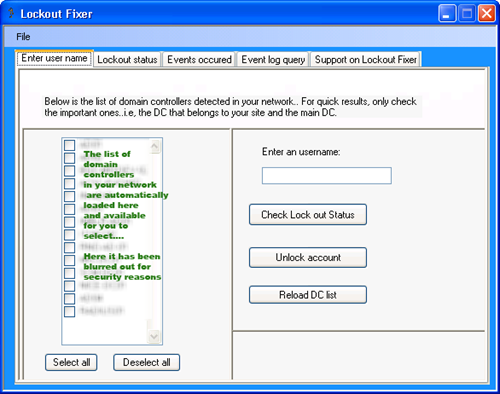
Lock out fixer is a free tool that helps administrators to troubleshoot the locking out of domain accounts. It works like the Microsoft tool Lockoutstatus.exe but in addition to just checking lock out time for all the domain controllers, it allows you to instantly view the audit failure logs written exactly at the time of the account lock out or bad password time.
Using Lock out fixer, the administrator can check the servers from the list of detected domain controllers, type in a username and then either unlock the account or check for the lockout status. The lock out status also displays the lock out time, last bad password time and bad password count for each of the domain controllers.

hi i try to use this application but it says i dnt have rights ...kindly help me to check i will send screenshot just provide your email address.....
ReplyDeleteThanks