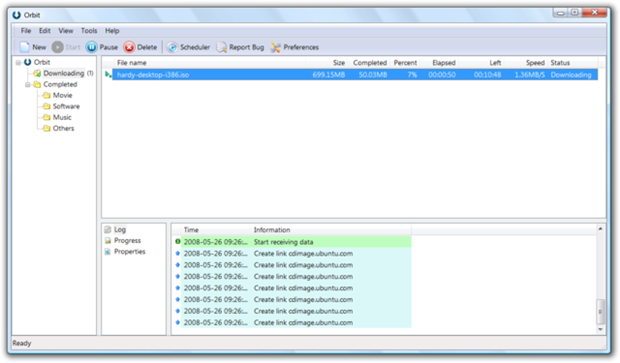
First launched in 2006, Orbit Downloader is a popular file downloading software that can integrate with nearly every popular web browser and speed up download of files over the Internet. With features like clipboard monitoring, peer-to-peer transfer to increase speed, and URL sniffing that enabled download of embedded videos from streaming websites made it one of the most successful download managers. Now a new research by security firm and anti-virus product manufacturer ESET has revealed that the program includes code designed to carry out distributed denial-of-service (DDoS) attacks on other machines.
The discovery came to light during a routine examination of the Orbit Downloader software package by the security firm. Apparently, when the main Orbit Downloader executable is run, it communicates with the orbitdownloader.com site, silently downloading a DLL file and a configuration file containing a list of targets to attack and a randomly-generated IP address for each.
The program then conducts either a SYN flood attack or a wave of HTTP connection requests on port 80 (the HTTP port) and UDP datagrams on port 53 (DNS). The IP address that accompanied the URL in the config file is used as the source address for the attack.
On a test computer set up in their lab with a gigabit Ethernet port, HTTP connection requests were sent at a rate of about 140,000 packets per second, with falsified source addresses largely appearing to come from IP ranges allocated to Vietnam. These blocks of IP addresses were hardcoded into the DLL file.
At this point, nobody is sure who is to blame for its possible that the servers of Orbit Downloader were compromised unbeknown to them, although its apparent that the author has gone to some lengths to hide the malware, as explained by ESET:
The first step is that files are encoded in base64, an encoding scheme most often used to send binary files as file attachments. After decoding, the data is then XORed with a fixed 32-character string. That 32-character string is actually the MD5 hash of a 9-character password that is hardcoded into the DLL file. After this operation, each pair of consecutive bytes are XORed together to generate a single byte of plaintext.
While each download of the encrypted data from the server varies, the actual content, once converted to plaintext, has remained constant for considerably longer periods of time.
The additional malware code appears to be added sometime between the release of version 4.1.1.14 (December 25, 2012) and version 4.1.1.15 (January 10, 2013).
Following this news, many file download sites including BetaNews, Softpedia, Softonic and MajorGeeks have all removed Orbit Downloader from their sites. If you are using this program, you should uninstall it too.

Soooo... any news on what legal action is being taken against the developers of Orbit Downloader?
ReplyDelete